



suspicious activity

cc6f1a04b10bcb168aeec8d870b97bd7c20fc161e8310b5bce1af8ed420e2c24

2[.]16[.]107[.]24

2[.]16[.]107[.]83

svchost.exe

malicious activity

5f94a66e0ce78d17afc2dd27fc17b44b3ffc13ac5f42d3ad6a5dcfb36715f3eb

biz9holdings[.]com,findresults[.]site,ww38[.]findresults[.]site
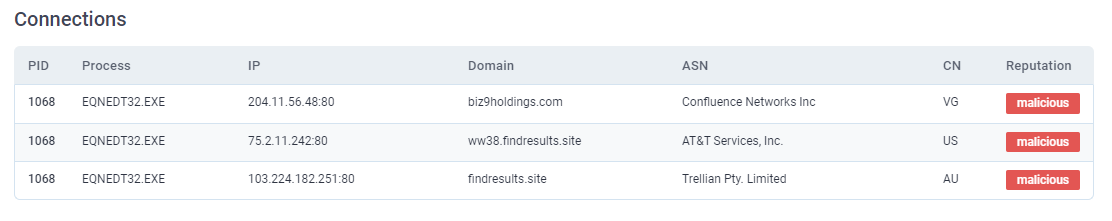
103[.]224[.]182[.]251,75[.]2[.]11[.]242,204[.]11[.]56[.]48


cve-2017-11882