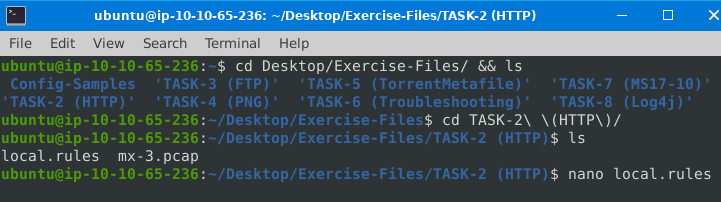
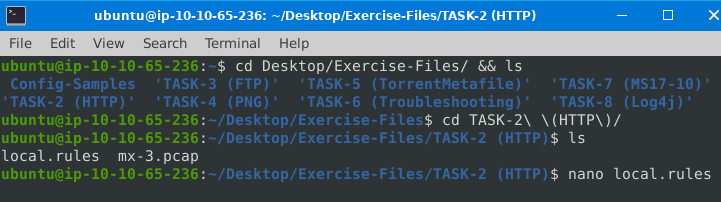

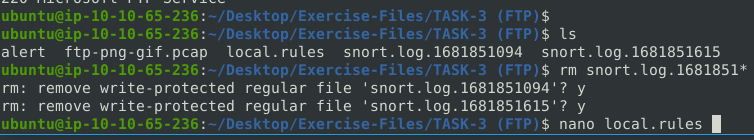
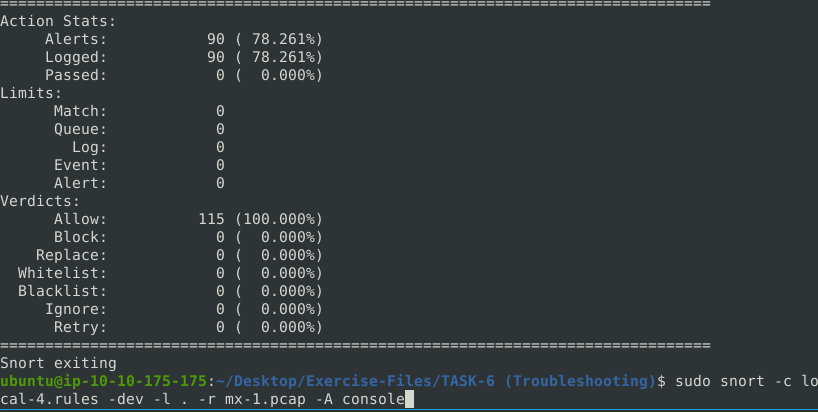
Command to create snort log using local rules

328
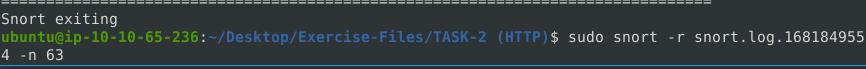
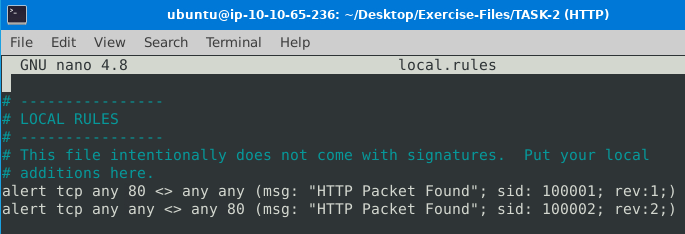
Command to analyze up to packet 63

145.254.160.237

Command to analyze up to packet 64

0x38AFFFF3

Command to analyze up to packet 62

0x38AFFFF3

Command to analyze up to packet 65

128

145.254.160.237

3372


FTP ALERTS

Command to create Snort log

614

grepping for FTP return code "Service Ready"


41
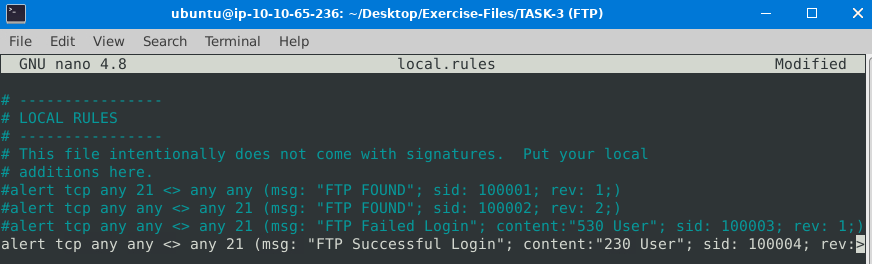

1


42

alert tcp any any <> any 21 (msg: "Failed Admin Login Attempt"; content:"Administrator"; content:"331 Password"; sid: 100005; rev: 1;)



List PNG file signature for content



Adobe Image Ready

List GIF file signature for content


GIF98a


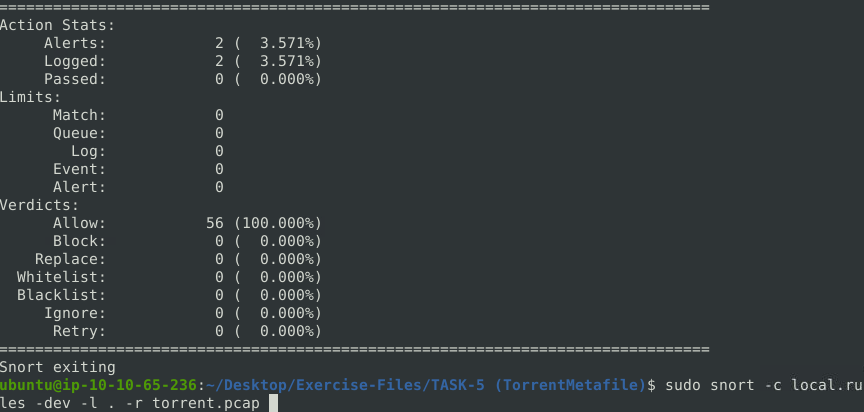

bittorrent

tracker2.torrentbox.com

any(msg:

any (msg:


sid: 1000001

16

Port value missing

68

GID SID in rule duplicates


87

Unmatch quote in rule option 'msg'

90

Illegal direction specifier


155

Change the direction to -> and the content in the rule to GET

2

alert does not have a msg set

25154


Bad escape sequence

removed \ in conent
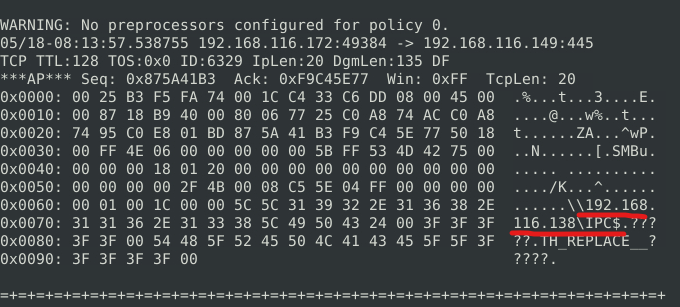
\\192.168.116.138\IPC


26

4

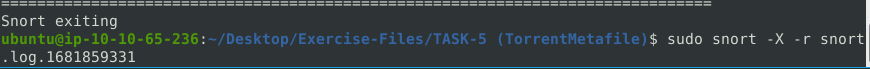
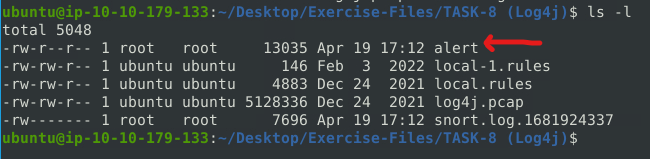
sudo snort -X -r snort.log.1681926058


